CCleaner has recently been infected with malicious software, which has alarmed many users since it is probably the most popular Windows cleaning software. If we were using version 5.33, then our computer might be infected. In this guide, we will show you how to check if you have the CCleaner malware on your system, and we will provide some useful tips to get rid of it.
Unblock any international website, browse anonymously, and download movies and Mp3 with complete safety with CyberGhost, just for $2.75 per month:
If you are not interested in learning what kind of malware it was or who it was targeting, you can skip directly to this part to see how to check your computer and clean any CCleaner-related infection.
How did the malware end up in CCleaner?
As you might know, Piriform is the company behind the development of CCleaner. However, in July 2017, Avast bought the company along with all of its products.
Not long after that, one or more hackers managed to breach into Avast's servers and infect CCleaner with a trojan. They probably integrated the malware into one of CCleaner's updates.

Avast claims that the hackers must have targeted Piriform long before they bought it, but that doesn't change the fact that the attackers used Avast's servers.
In a scale from 0 to 10, how ironic do you think it is that CCleaner got infected with malware only one month after an antivirus company bought it?
An antivirus company ending up distributing malware; we think it is worth at least an 8.
Anyway, the infected CCleaner version is the 5.33.6162, released on August 15th. For four weeks, nobody realized that the program installed a trojan on the user's system.
Morphisec was the company that first noticed the problem on September 12th. They informed Avast, which took all the necessary steps to suppress the threat. They immediately released version 5.33.6163, which was a small update aiming to fix the problematic version. In fact, the only difference from 5.33.6162 is the absence of the trojan.
Until now, there have been even more updated versions, and CCleaner's most recent is 5.35. Avast has also confirmed that the malware is not present on the next CCleaner editions, from 5.34 onwards.
What kind of virus was the CCleaner malware
Now the question is, what did this malware do to the infected machines? Who were its targets? Should we worry?
As soon as they discovered the problem, Cisco's Talos team analyzed the threat and deducted it was not targeting home users.
For those not familiar with Talos, let's just say that it is a group that gathers information about existing online threats and offers protection from viruses and malware.
The first payload
According to Talos' analysis, the malware was designed to collect the following information:
- The computer's name
- The MAC address of up to three network adapters
- A list of installed programs and Windows updates
- The processes running at the given moment
- Other system information, such as the OS architecture (32-bit or 64-bit), administrator privileges, and so on.
Then, the trojan used a C2 server to upload the information it collected and download the first payload to the user's computer.
If you're interested in reading Talos' detailed analysis of the CCleaner malware, visit this link.
The second payload
As it seems, the trojan wouldn't stop there. The next step was to download the second payload to the infected system. Thus, on September 20th, the Talos team came up with a second analysis of the CCleaner malware.
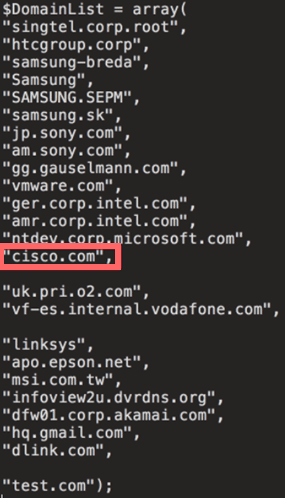
Among other things, they state that the primary target of the attackers was a list of famous companies and brands. Among them, we can see Samsung, Sony, and even Cisco.
Here you can read the second report.
How many users were infected?
If we take into account the download rate of CCleaner on Piriform's website, then the number of users infected could be enormous.
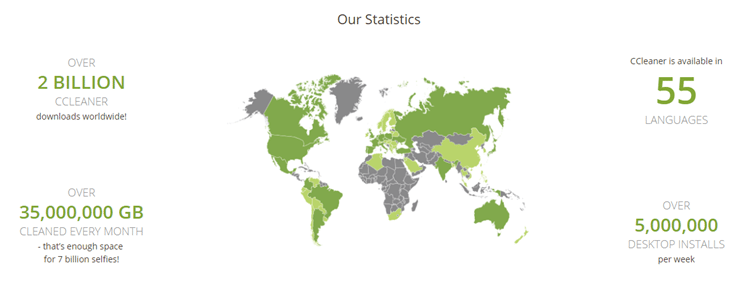
As we can see, the company reports over 2 billion downloads worldwide, and over 5 million installations each week.
Fortunately, the users that might have been infected are much fewer, as only two of CCleaner's products contained the trojan; the 32-bit Windows version and the cloud versions.
The total number of computers initially affected was around 2.27 million. By September 18, the systems still using the infected CCleaner that were affected by the second payload are estimated to be about 730.000.
Of course, Avast disabled the malware server-side, so people that are still using version 5.33, they are entirely safe; at least that's what Avast claims in their report.
How to check if the CCleaner malware is on your computer
Although we are not at risk, even with version 5.33, it is a good idea to locate the malware and remove it - if we got infected in the first place.
The first thing we need to do is look at the version of CCleaner installed on our computer. We can open the program and check in the upper left corner.
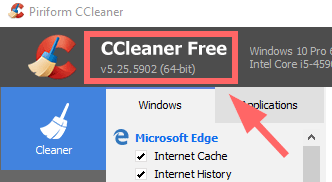
Even if we have an older version than 5.33, it is a good idea to update it and install the newly 5.35, which we can download from Piriform's website.
If we use the cloud version of CCleaner, the virus is in version 1.07.3192.
Check Windows registry
Besides the release version, we can also take a look at our Windows registry and see if we can find any suspicious entries.
We press the Windows key along with R to open Run command, and we type "regedit."
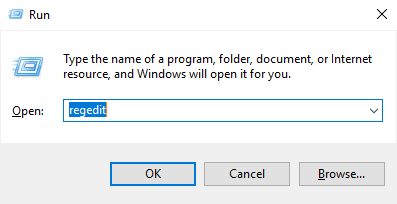
Once we are in the registry editor, we go to the following location:
HKEY_LOCAL_MACHINE \ SOFTWARE \ Piriform \ Agomo
In that folder, we check at the right if we can see any value with the name MUID, TCID, or NID.
A clean version of CCleaner won't generate those values. If you can see them in your registry, it means your computer got infected at some point.
The same goes for this path:
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\WbemPerf
Here, we are looking for values 001, 002, 003, 004, and HBP. Their existence is a strong indication that we have the malware.
Furthermore, it is worth mentioning that, although the trojan works correctly only on 32-bit systems, the above values are also created on 64-bit versions of Windows.
What should I do if I have the CCleaner malware?
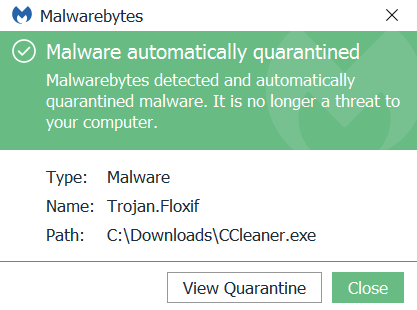
An anti-malware is the best course of action if we are infected. Malwarebytes, for example, can identify the threat and put it to quarantine.
If you suspect that you have the trojan, or if you just want to be on the safe side, you can download Malwarebytes from here.
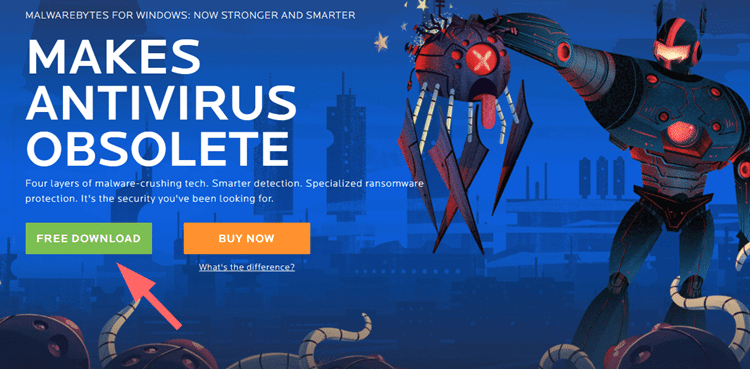
After a quick scan, almost any anti-malware program will detect the file as Trojan.Floxif and automatically quarantine it.
The second payload is related to Trojan.Famberp, which anti-malware apps detect it the same way. Other files related to the threat that are likely to be removed are the following:
- GeeSetup_x86.dll (Hash: dc9b5e8aa6ec86db8af0a7aa897ca61db3e5f3d2e0942e319074db1aaccfdc83)
- EFACli64.dll (Hash: 128aca58be325174f0220bd7ca6030e4e206b4378796e82da460055733bb6f4f)
- TSMSISrv.dll (Hash: 07fb252d2e853a9b1b32f30ede411f2efbb9f01e4a7782db5eacf3f55cf34902)
System restore
Due to the second payload, Cisco suggests we should restore our system from a restore point before the infection, should we have one.
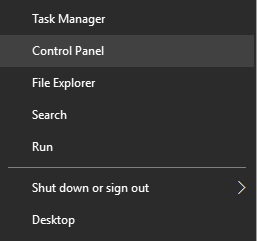
To access System Restore, right-click on Start and choose Control Panel.
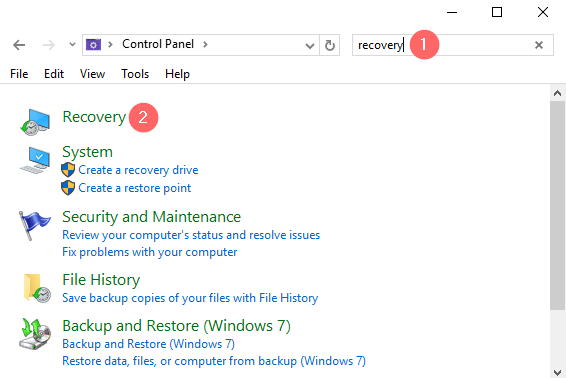
Type "recovery" on the search bar and click on it.
Go to "Open System Restore" and press "Next."
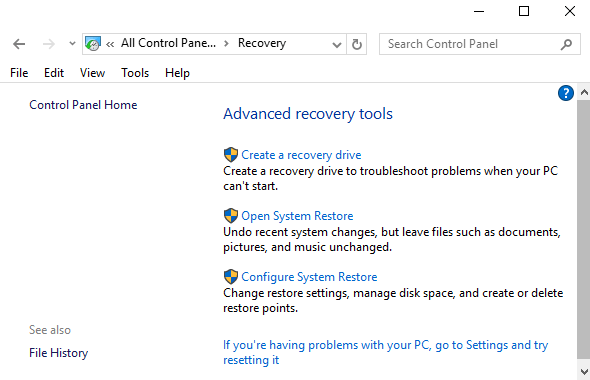
From there, choose a restore point before August 15, and follow the steps to finish the restore.
Is CCleaner safe?
The new versions of CCleaner are safe, so we can keep using the program.
However, it turns out that even the most familiar and trusted applications can sometimes contain dangerous software. If you want to avoid any third-party cleaning apps, you can always set up your computer to clean automatically.
Did the CCleaner malware infect your machine?
Did you find any suspicious threat on your computer? If so, did you manage to get rid of it with the steps we mentioned above?
If you face any other problems or if you have anything to add, feel free to leave a comment.
Support PCsteps
Do you want to support PCsteps, so we can post high quality articles throughout the week?
You can like our Facebook page, share this post with your friends, and select our affiliate links for your purchases on Amazon.com or Newegg.
If you prefer your purchases from China, we are affiliated with the largest international e-shops:




Leave a Reply